Insights
/
feb 16, 2025
Harvest Now, Decrypt Later: A Future Threat Businesses Can’t Ignore
Attackers are collecting encrypted data today to decrypt in the future. Learn what “harvest now, decrypt later” means and how to reduce the risk.
/
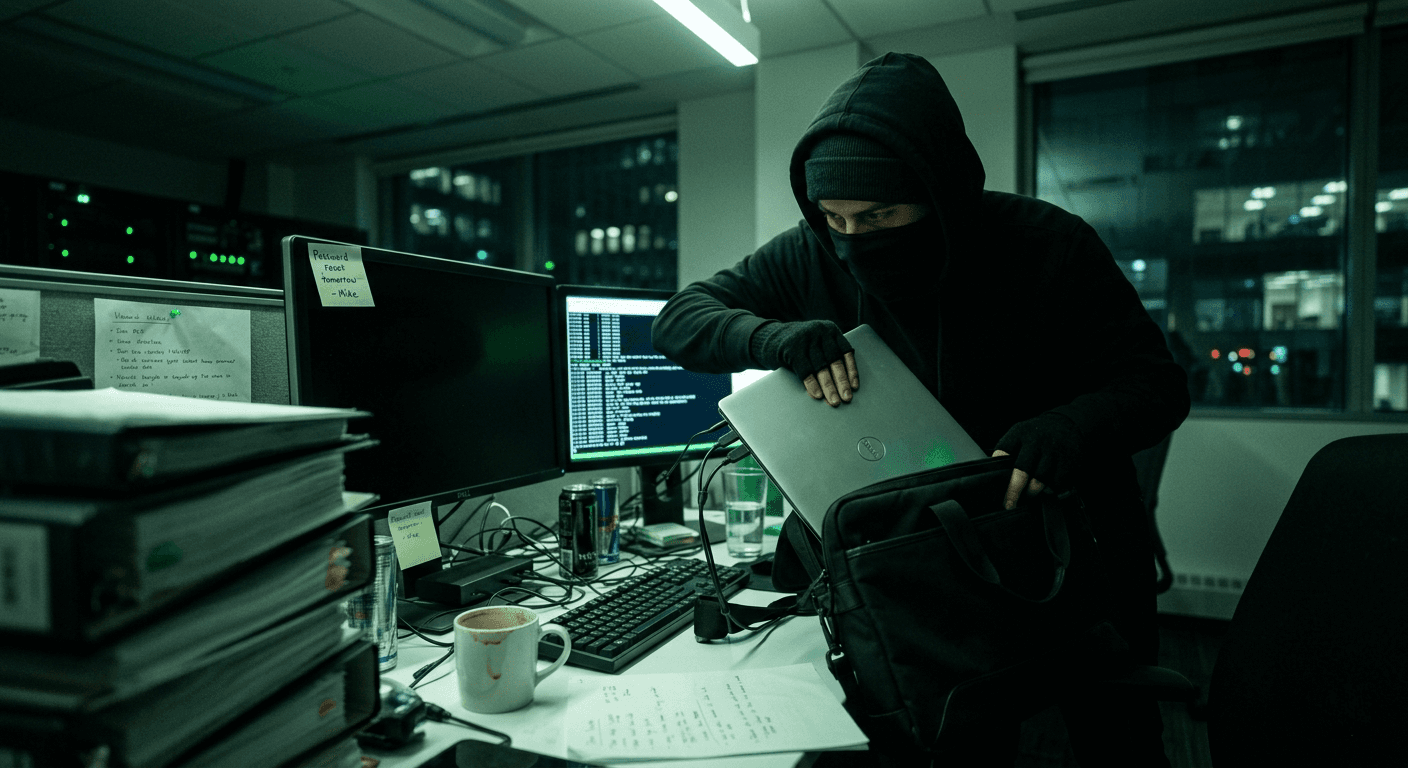
AUTHOR
SolveCyber

Imagine your sensitive business data is stolen. If it's encrypted, then the threat is minimal. However, what if the intention isn't to use it now, but to store it for future use. While current encryption is secure, future advances in computing, particularly quantum computing, may render today's encryption useless. Sophisticated attackers have realised this and have already started collecting this encrypted data for decryption sometime in the future. This is the idea behind “harvest now, decrypt later” (HNDL), it’s a growing concern in cybersecurity, let's unpack it.
What Does “Harvest Now, Decrypt Later” Mean?
Most sensitive data today is protected using strong encryption. This includes:
Emails and communications
Financial data
Customer records
Cloud storage
Encryption works by using mathematical algorithms that are currently extremely difficult to break.
However, attackers are already collecting encrypted data now, with the intention of decrypting it later when more powerful computing methods become available.
Even if the data is secure today, it may not be secure forever.
Why This Matters for Businesses
Not all data loses value over time.
Some information remains sensitive for years, including:
Personal and identity information
Health records
Intellectual property
Legal and financial documents
If this data is stolen today and decrypted in the future, it can still cause:
Regulatory and legal issues
Reputational damage
Loss of competitive advantage
For organisations handling long-lived sensitive data, this is a real risk.
The Technical Risk
Many current encryption standards rely on mathematical problems that are difficult for classical computers to solve.
Future technologies, particularly quantum computing, may be able to solve these problems much faster, potentially making some encryption methods obsolete.
This means that data encrypted today using current standards could eventually be decrypted if it is captured and stored by attackers.
What Businesses Can Do
While this threat is future-focused, there are practical steps organisations can take now.
Identify Long-Lived Sensitive Data
Understand what data needs to remain secure for many years. This helps prioritise what requires stronger protection.
Minimise Data Exposure
Reduce how much sensitive data is stored, transmitted, or retained. The less data available, the lower the long-term risk.
Use Strong, Modern Encryption
Ensure current systems use up-to-date encryption standards and best practices.
Plan for Cryptographic Agility
Systems should be designed so encryption methods can be updated as standards evolve, without major disruption.
Secure Data at Rest and in Transit
Ensure encryption is applied consistently across storage, backups, and communications.
A Risk That Starts Today
“Harvest now, decrypt later” is not a future problem — it starts with data being collected today.
While the ability to break modern encryption is likely still years away, organisations that handle sensitive, long-lived data need to start thinking about how that data is protected over time.