Insights
/
feb 16, 2025
Inside the Medibank Breach: How Millions of Health Records Were Exposed
The Medibank cyber attack exposed sensitive health data of millions of Australians. Here’s how the breach unfolded and what businesses can learn.
/
AUTHOR
SolveCyber
Late in 2022, one of Australia’s largest health insurers found itself at the centre of a crisis.
Customers of Medibank began receiving notifications that their personal information may have been stolen. At first the situation seemed uncertain — a cybersecurity incident, possibly involving stolen data.
Within weeks, it became clear that something far more serious had happened.
Attackers had gained access to Medibank’s systems and extracted sensitive personal and health information belonging to millions of Australians.
It would become one of the most significant data breaches in the country’s history.
The Quiet Beginning
The attack did not start with dramatic hacking scenes or sophisticated exploits.
Instead, the attackers reportedly gained access to the company’s environment using stolen login credentials.
Once inside, they were able to move through internal systems, locate databases containing customer records, and begin extracting large volumes of information.
For weeks, the activity remained largely unnoticed.
By the time the breach was fully understood, the attackers had already taken enormous amounts of data.
What Was Stolen
The scale of the breach shocked both regulators and the public.
The stolen information reportedly included:
Names and dates of birth
Contact information
Passport and identification details
Health claims information for some customers
Unlike many other breaches, the data included extremely sensitive medical information, raising concerns about privacy, extortion, and long-term misuse.
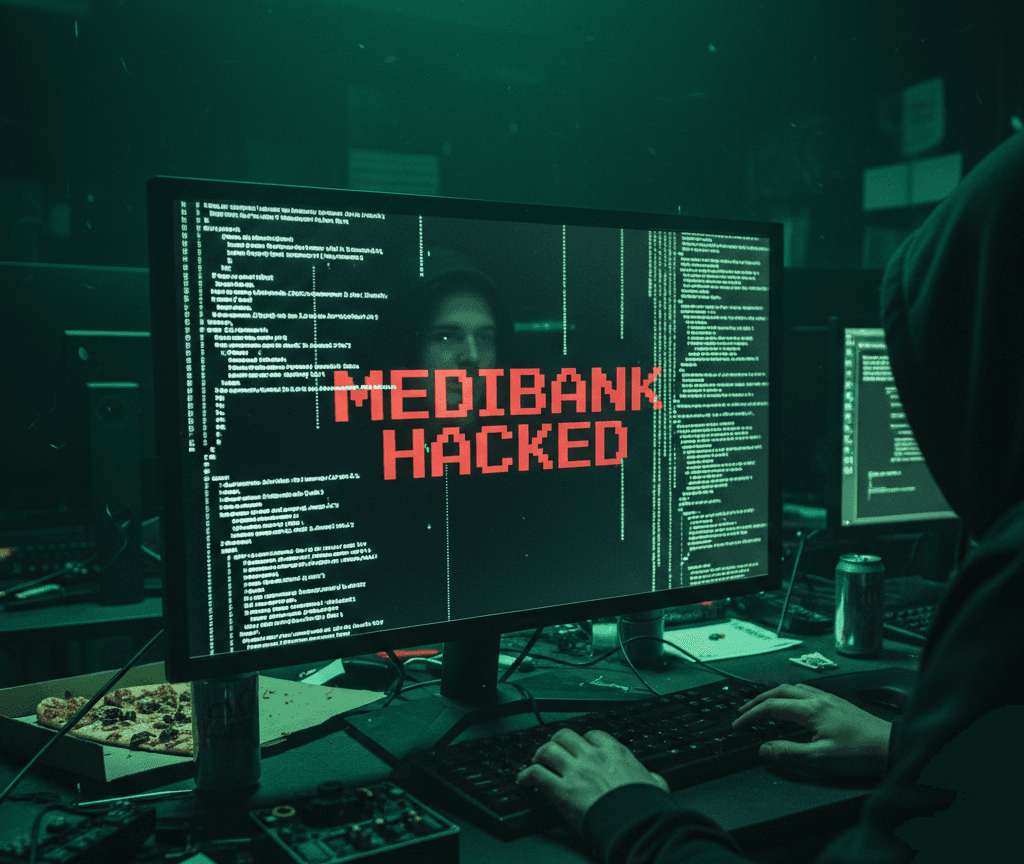
Soon after the breach was disclosed, the attackers began releasing portions of the stolen data online.
The message was clear: pay the ransom, or the data would continue to be published.
The Ransom Decision
The criminals demanded payment to prevent further releases.
But Medibank made a difficult decision.
The company announced it would not pay the ransom, arguing that paying criminals could encourage further attacks and there was no guarantee the stolen data would actually be deleted.
Instead, the organisation began working with law enforcement and cybersecurity experts to respond to the breach.
In the weeks that followed, some of the stolen data was released online anyway.
The Impact on Customers
For the millions of Australians affected, the breach was deeply personal.
Unlike many cyber incidents that involve email addresses or passwords, this breach exposed health-related information — something many people consider among the most private data they have.
Customers worried about identity theft, fraud, and the long-term exposure of personal medical details.
The breach also triggered investigations by regulators and prompted widespread discussions about how organisations protect sensitive data.
A Lesson for Businesses
The Medibank incident highlights a reality that many organisations face today: attackers do not always need complex technical exploits to cause major damage.
Often, a single compromised account is enough to open the door.
Once inside a network, attackers can explore systems, access sensitive databases, and quietly extract information over time.
The technical entry point may be simple, but the consequences can be enormous.
The Bigger Picture
Cyber attacks are no longer rare events targeting only technology companies. Organisations across every sector — healthcare, finance, logistics, and retail — now hold large amounts of valuable digital data.
For attackers, that data is the prize.
The Medibank breach serves as a reminder that protecting systems, monitoring access, and regularly testing security controls are critical steps in preventing similar incidents.
Because when sensitive data is exposed, the damage extends far beyond the network where the breach began.
At SolveCyber, we provide engaging staff cybersecurity training to help your team recognise threats and stop attacks before they start.