Insights
/
feb 16, 2025
Why You Need an Outsider’s View of Your Security
Internal teams miss what attackers see. Learn why independent penetration testing and external assessments are critical to finding real security risks.
/
AUTHOR
SolveCyber

Most organisations believe they have a good handle on their cybersecurity.
They know their systems. They trust their controls. They rely on internal teams to manage risk.
But attackers don’t see your environment the way you do.
They see it as an outsider.
And that difference matters.
The Problem With Internal Assessments
Internal teams are close to the systems they build and manage. Over time, this creates blind spots.
Processes feel secure because they are familiar. Assumptions go unchallenged. Small risks are overlooked because “they’ve always been that way.”
Even highly capable teams can miss vulnerabilities simply because they are too close to the environment.
Security assessments performed internally often validate what is already believed — rather than uncovering what is actually exposed.
How Attackers Really Think
Attackers don’t follow internal processes or documentation.
They test assumptions. They look for misconfigurations. They try things that “shouldn’t work.”
They approach systems with no bias and no constraints.
This is exactly what makes an external perspective so valuable.
An outsider looks at your environment the same way an attacker would — without assumptions, and with the goal of finding weaknesses.
What External Testing Finds
Independent penetration testing often uncovers issues that internal teams miss, such as:
Misconfigured access controls
Exposed services or APIs
Weak authentication or password policies
Chained vulnerabilities that create larger risks
These are not always complex technical flaws. Often, they are small gaps that combine into real attack paths.
The Business Impact
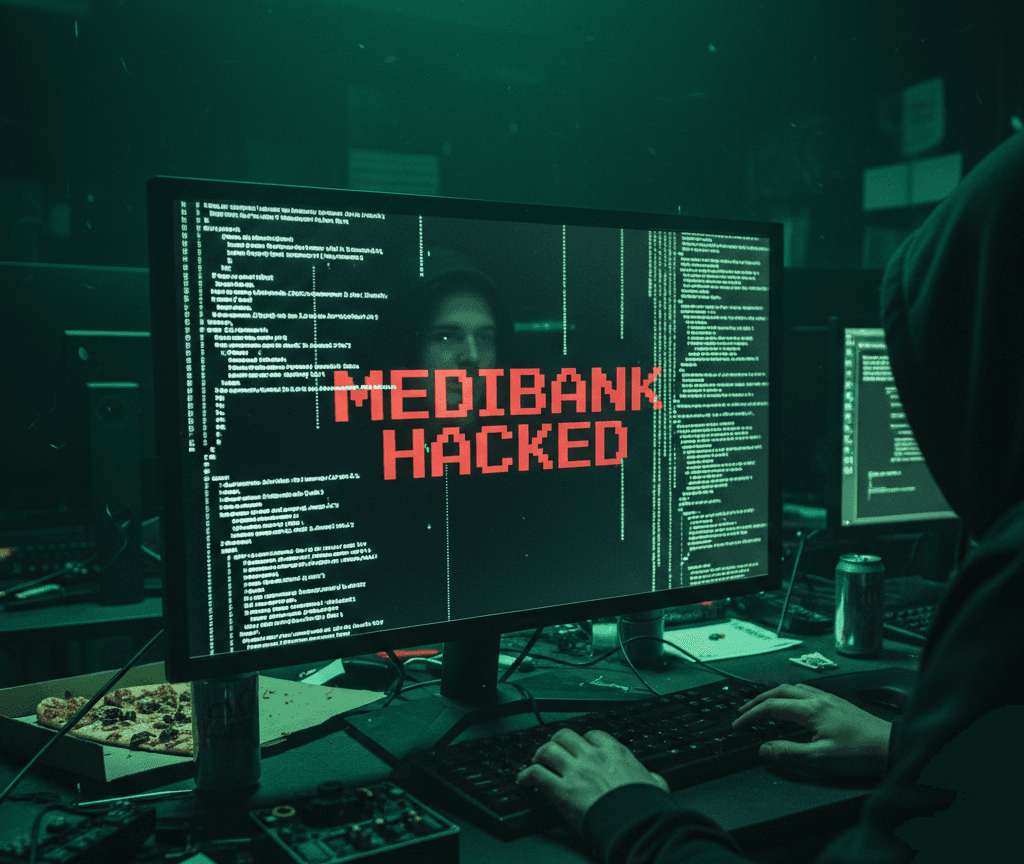
Undetected vulnerabilities can lead to:
Data breaches
System compromise
Financial loss
Reputational damage
The cost of an external assessment is small compared to the cost of a real incident.
More importantly, it provides confidence — knowing that your security has been tested from an attacker’s perspective.
Why Penetration Testing Matters
Penetration testing goes beyond automated scanning or checklist-based reviews.
It involves real people actively attempting to compromise systems, identify weaknesses, and demonstrate how an attacker could gain access.
This human-led approach is what makes it effective.
It answers a critical question:
“If someone tried to break into our systems, how would they do it?”